Many T-Mobile and AT&T subscribers could have been victims of a "SIM swap"
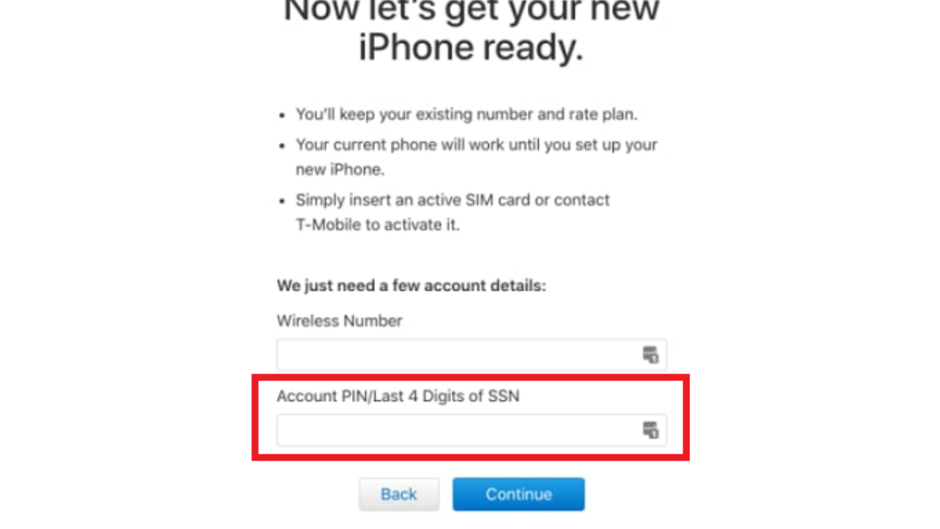
T-Mobile customers purchasing an Apple iPhone from Apple's online store have to enter a four-digit PIN number or the last four digits of their social security number if they plan on financing the device (view image at the top of this article). For some reason, the page used to allow an infinite number of attempts to punch in the correct numbers which made the platform vulnerable to brute force attacks. And once a hacker has his hands on a T-Mobile customer's PIN number, or last four digits of a customer's social security number, he can request a new SIM card tied to the victim's T-Mobile account. At that point, not even two-factor authentication would be able to save the T-Mobile subscriber from having accounts connected to a smartphone from getting cleaned out.
In case you were wondering, AT&T, Verizon and Sprint subscribers financing the purchase of a new iPhone from Apple's online store once had more protection from brute force attacks than T-Mobile subscribers. After five to ten incorrect guesses at the PIN number or last four digits of the social security number, a hacker has just 60 minutes to find the correct digits. A perfect solution? No, but it is better than infinite guesses.
77 million T-Mobile subscribers were exposed due to this vulnerability. AT&T also had a similar issue revealed this week when it was discovered that the website for phone insurer Asurion released PIN codes belonging to AT&T customers. This security flaw could have allowed a hacker to request a new AT&T SIM card, thus giving the thief unlimited access to a victim's handset.
"Asurion takes customer security and privacy very seriously, and as such we have an ongoing, layered security program in place to prevent security issues. We are investigating the researcher’s concerns, but have immediately implemented measures to address these concerns to ensure customers’ accounts are safe."-Nicole Miller, spokesperson, Asurion
As it turns out, both Apple and Asurion made the necessary changes to their websites. But it does show that carriers around the world need to make it harder to obtain replacement SIM cards. Additionally, carriers in general must beef up security, including using background checks from legit security firms to check out newly hired employees. Several incidents involving the theft of bank and cryptocurrency accounts were made possible with the help of rogue employees working for wireless providers. These insiders funneled personal account information to the thieves in exchange for cash.
Follow us on Google News












Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: