28 Android apps delivering bogus information were installed 7 million times from Google Play Store
Making matters worse, those who wanted what they thought was valid data had to pay for it first.

Apps in Play Store deliverng bogus data were installed 7 million times. | Image by PhoneArena
Security research firm ESET named 28 fraudulent apps found in the Google Play Store CallPhantom because they all claimed to allow users access to call histories, WhatsApp call logs, and SMS records for any phone number. All together, these apps were installed 7.3 million times by Android users.
CallPhantom apps were installed 7.3 million times from the Google Play Store
What those who installed the apps had to do was pay for the information, and it wasn't even legitimate data they received. So what did these Android users get in return for their hard-earned cash? Would you believe that all they got was randomly generated data?
Since ESET is an App Defense Alliance partner, it was forced to report what it had discovered to Google. The latter did the right thing and removed the apps mentioned in ESET's report from the Google Play Store. Because some of the 28 apps were able to escape the Play Store's official billing system, it was difficult for Google to arrange refunds to some victims of this scam.
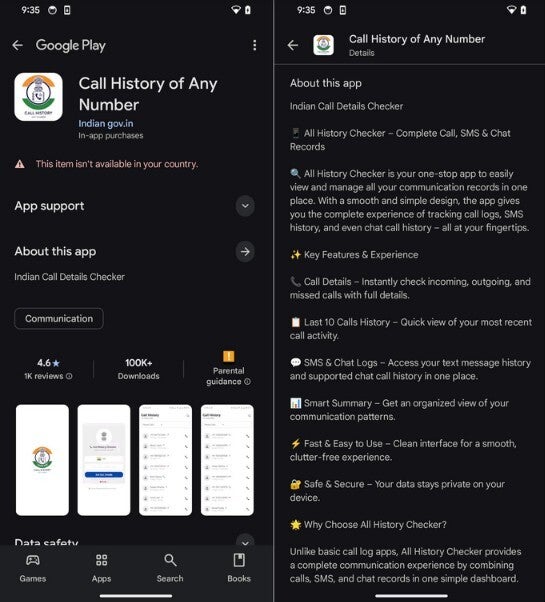
Google Play Store listing of one CallPhantom app. | Image by ESET
Last December, ESET became aware of an app titled Call History of Any Number found in the Google Play Store. The app claimed to give users the call history for any phone number, and despite the developer's name of Indian gov.in, the app had no connection with the Indian government.
Data generated by these apps was bogus and fabricated by each app
Which type of malware worries you the most?
ESET discovered that the call numbers that were supposedly part of the call history generated for a phone number you supplied the app with, were all fake and random numbers generated by the app. These randomly-generated numbers were matched with fixed names, call times, and call durations that were embedded inside the code.
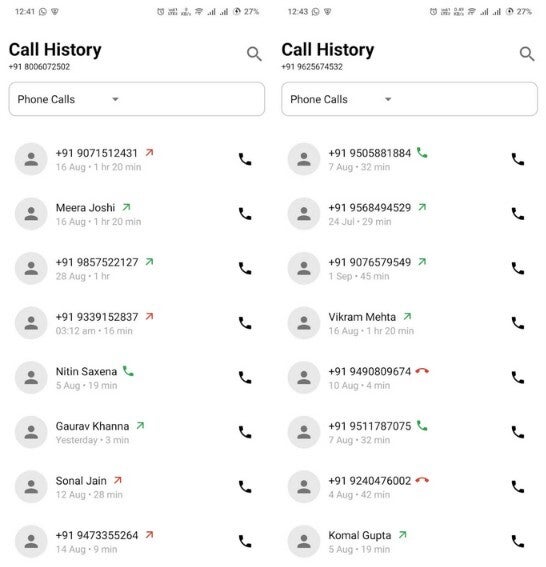
The lists of names and numbers delivered by the apps were fake. | Image by ESET
The data was turned over to those who had installed the app on their Android devices, but only once they paid for the service. The Play Store listing for the app also used a screenshot showing the fake code that was designed to make Android users believe that the app really worked.
ESET eventually found a total of 28 related apps in the Google Play Store. The set of 28 apps was reported to Google on December 16, 2025. All reported apps have been removed from the Play Store.

Some of the CallPhantom apps found in the Play Store. | Image by ESET
While the 28 related apps used different designs to appear as though they were not related to each other, ESET said that they all had the same goal which was to "generate fake communication data and charge victims for access."
Android users in the world's second-largest smartphone market were targeted by the scam
The listings in the Play Store related to the "CallPhantom" apps targeted Android users in the world's second-largest smartphone market, India. Many of these apps came with India's +91 country code pre-selected and worked with a payment system called UPI that works mostly in India.
You might recall that many times in the past I have told you to look at the comments section when installing an app from a developer who you are not familiar with. That is where you will find red flags discussed by people who actually installed the apps.
In this case, looking at the comments before installing and paying for a subscription, probably would have saved you time and money. One comment says that the app is fraud and shows random names instead of giving real call histories. That commenter nailed it perfectly.
The apps even had a way to trick users into paying for the bogus data
Another comment warned others that the app "is a scam completely," while another accurately stated that "fake numbers appear every time." That's because the app has no functionality that would allow it to collect real call, SMS, and WhatsApp data.
While some of the apps used the Google Play Store's official billing system and thus were able to send out refunds, others used third-party apps that support UPI. Other apps used payment card checkout forms that were found in the CallPhantom apps.
Subterfuge was also used to trick those who installed a CallPhantom app into paying for the service. If a user exited the app without paying for the service, a fake email alert would show that call history results had arrived. Clicking the notification would take you to a page where you could subscribe. While prices varied from app to app, the highest cost was $80 USD while the lowest was €5.











Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: