Delete this popular video app now or else you might get charged for services you didn't request
Just the other day we warned you about 15 Android apps that need to be deleted from your phone; these apps contain adware that play screen-length ads on Android handsets generating revenue for a bad actor. And because these apps' icons disappear from the app drawer, uninstalling them is a very complicated task. And once again our early warning indicator-the comments section on the Google Play Store listing-flashed blinking red lights.
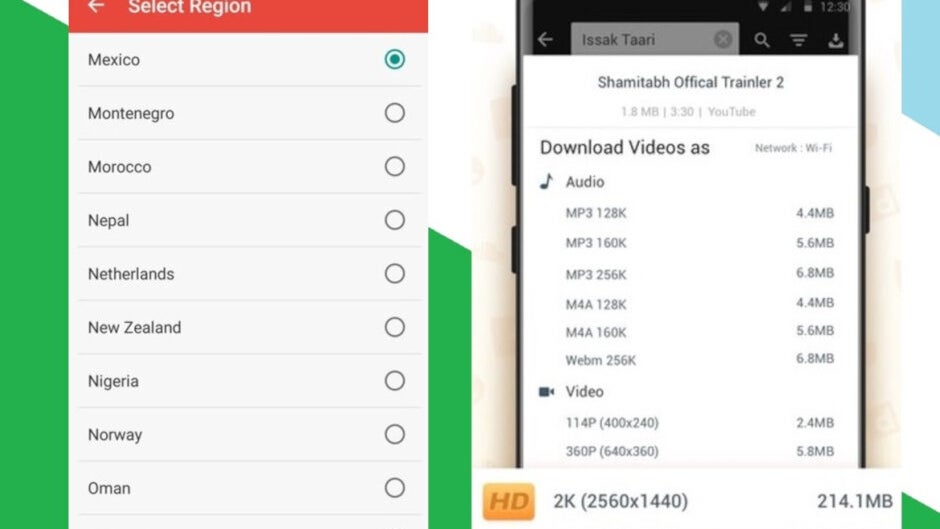
Now, U.K. security firm Upstream (via Tech Crunch) has discovered that an Android app with a whopping 40 million users, has been engaging in "suspicious transactions" without the knowledge of those who installed the app on their device. The app, named Snaptube, allows users to download any video from YouTube so that it can be viewed offline. Upstream's Secure-D platform, which detects and blocks fraudulent online transactions, has blocked 70 million fraudulent transactions originating from Snaptube just over the last six months. According to the security firm, had that suspicious activity not been red-flagged, 4.4 million consumers would have been out more than $90 million dollars for premium digital services that they never ordered.
Snaptube claims that its reputation is also a victim
In addition to signing up users for premium services that they didn't want, Snaptube also automatically clicks on ads in the background enriching the bad actors involved in creating the malware. Upstream's CEO, Guy Krief, says, "Only the app downloads and clicks on the adverts. Nothing is shown on the handset screens. The video app is literally a screen for the suspicious background activity." He went on to add, "We are blocking new threats every day and we would advise anyone using the Snaptube app to carefully watch their phone bills and report to their operator any subscriptions or charges that they did not authorize." Upstream ran some tests that prove the app can "serve up and respond to advertising in the background without its users’ consent or knowledge."
Upstream says that Snaptube contains the same developer software code, Mango SDK, used by another popular Chinese based video app called Vidmate. Those installing the latter were also getting charged for premium subscription services that were not ordered. And both Vidmate and Snaptube have similar URLs, domains and traffic patterns. According to Upstream, those in Brazil, Egypt, Sri Lanka, Malaysia, and South Africa are most affected by Snaptube. The app is only offered through third-party app stores and is not listed in the Google Play Store.

Traffic patterns of Vidmate and Snaptube
Snaptube has responded to these allegations by stating that it was a victim too. It claims that "We didn’t realize the Mango SDK was exercising advertising fraud activities, which brought us major loss in brand reputation. After the user complained about the malicious behavior of the Mango SDK, we quickly responded and terminated all cooperations with them. The versions on our official site as well as our maintained distribution channels are free of this issue already." Those behind Snaptube say that they are thinking about taking the developers of Mango SDK to court.
But this is not the first time that the Snaptube app has engaged in questionable behavior. Back in February, security firm Sophos issued a report that charged Snaptube with different types of fraudulent behavior such as playing ads in the background that are invisible to the phone's user and creating fake app clicks. Both of these are designed to bring in revenue to the bad actor. As of February, when Sophos wrote its report, it had calculated that over the period of time that it was tracking it, the Snaptube app was updated more than 3,000 times. That works out to an average of 2.5 updates per day! Sophos was told in August that Snaptube was removing this code from the app, but months later this has yet to be done.
According to the official Snaptube website, the app, developed by Chinese firm Mobiuspace, has 40 million active daily users and has amassed 15 million likes.













Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: