Once again we implore you to delete this malicious Android app

Over the last few years, we have written about malicious Android apps that were created to make money for the attacker while negatively impacting a user's Android phone. Some of these apps run video ads in the background allowing a bad actor to collect big bucks. Other apps secretly send texts through premium messaging services or sign up users to other premium services that the hackers profit from.
Bad actors are reportedly taking advantage of the pandemic to rip-off Android users
There are many different ways that these malicious apps can squeeze money out of a phone. In Brazil, Android phone owners use prepaid credit to sign up for services. This gives the bad guys an opportunity to subscribe Android users to premium services without their knowledge. And while Google says that its Google Play Protect keeps an Android handset safe 24/7, that doesn't seem to be the case.
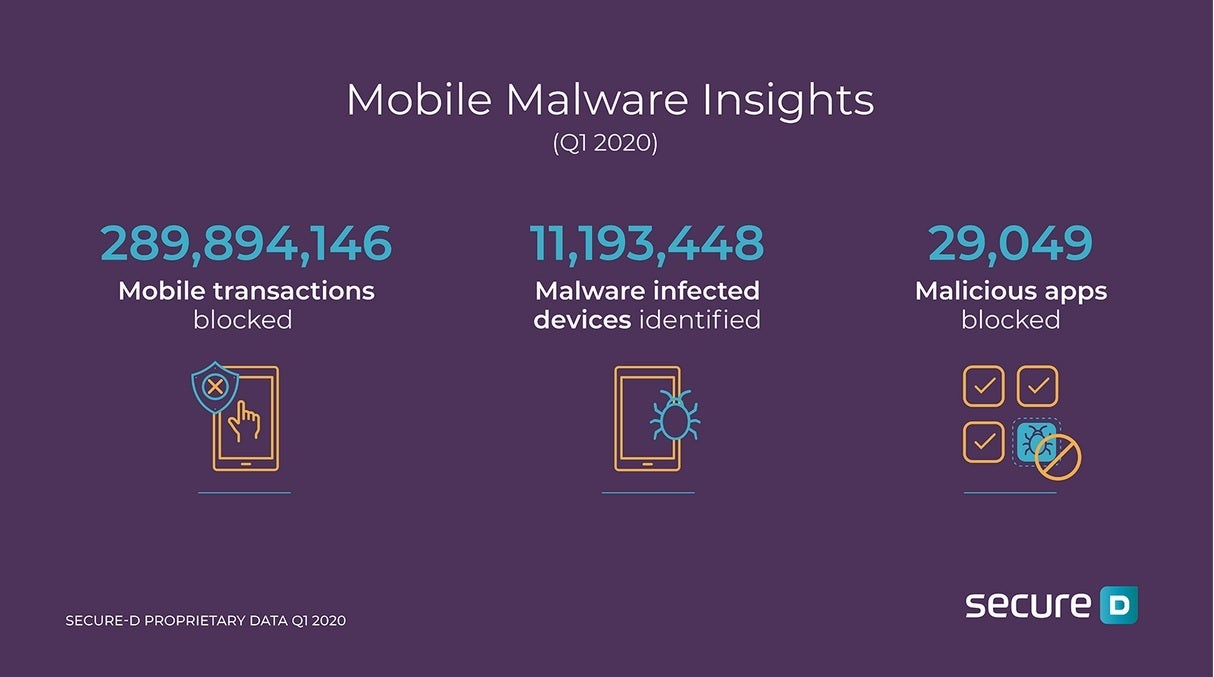
Nearly 290 million transactions from malicious Android apps were blocked in Q1 2020
A new report from Upstream says that in the first quarter, the number of Android apps it considers to be malicious doubled year-over-year from over 14,500 to more than 29,000. Transactions it describes as fraudulent rose 55% during the same time period as it blocked nearly 290 million transactions. 89% of the total number of transactions presented from January through March were fraudulent according to Upstream. The latter's Secure-D platform spotted a hike of 7% in the number of "infected" Android devices during the first quarter from 10.5 million to 11.2 million year-over-year.
Amazingly, nine out of the top 10 malicious Android apps during the first quarter of this year were available on the Google Play Store at some point during the three month period. Last year, 30% of the top 100 malicious apps were found on Google's Android app storefront. Interestingly, the bad actors are taking advantage of the global pandemic. During 2020's first three months, 60% of malicious apps could be considered "leisure" apps providing users with something to do while stuck at home. These apps fit into categories that include "video players & editors," "news & magazines," and "games" and "social." UPDATE (July 27, 2020): Here's a fresh list of newly discovered malicious android apps you need to delete from your phone.
For example, Upstream says that the most troublesome app is video downloader Snaptube. We warned you about this app back in October and it now has been installed over 40 million times. Once installed on an Android phone, Snaptube signs up victims for premium service that they didn't ask for and also downloads and clicks on ads that the app generates. Last year 70 million fraudulent transactions were generated by Snaptube (half of these in Brazil) with another 32 million blocked so far this year.
Snaptube's own website claims that the app has over 300 million users although it has been removed from the Google Play Store. It is available from Huawei's AppGallery app storefront, Xiaomi's GetApps store, and other app stores.
Snaptube's own website claims that the app has over 300 million users although it has been removed from the Google Play Store. It is available from Huawei's AppGallery app storefront, Xiaomi's GetApps store, and other app stores.
The head of the Secure-D platform at Upstream, Geoffrey Cleaves, says, "With the majority of the world having shifted indoors, there were some darker forces acting to make a profit from the lockdown situation. At Secure-D, we’ve seen a sharp increase in bad actors publishing 'leisure' apps on the Google Play Store, which trick users into subscribing for premium services." We aren't looking to pick on Android over iOS, but Upstream says that Android happens to be easier for hackers to work with. That's because the operating system supports the sideloading of apps through third-party app stores.
Upstream's Cleaves, discussing COVID-19's effect on malware, says, "Being in lockdown means prepaid customers will find it difficult to get out the front door to top up their data bundles. In the meantime, malware could be eating into those data bundles. I suspect we may see a drop in mobile internet traffic, and successful billing attempts, in predominantly prepaid developing markets while lockdowns are in force."













Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: