Android vulnerability allowed for PNG files to execute malware
With smartphones becoming a central hub for our lives and being used for financial transactions on a daily basis, hackers are always looking for ways to gain access to them so they can be used for nefarious purposes like stealing personal data, credit card numbers and so on. This is why it is so important for smartphones to receive regular security updates and for the operating system’s developers to find vulnerabilities and fix them as soon as possible.
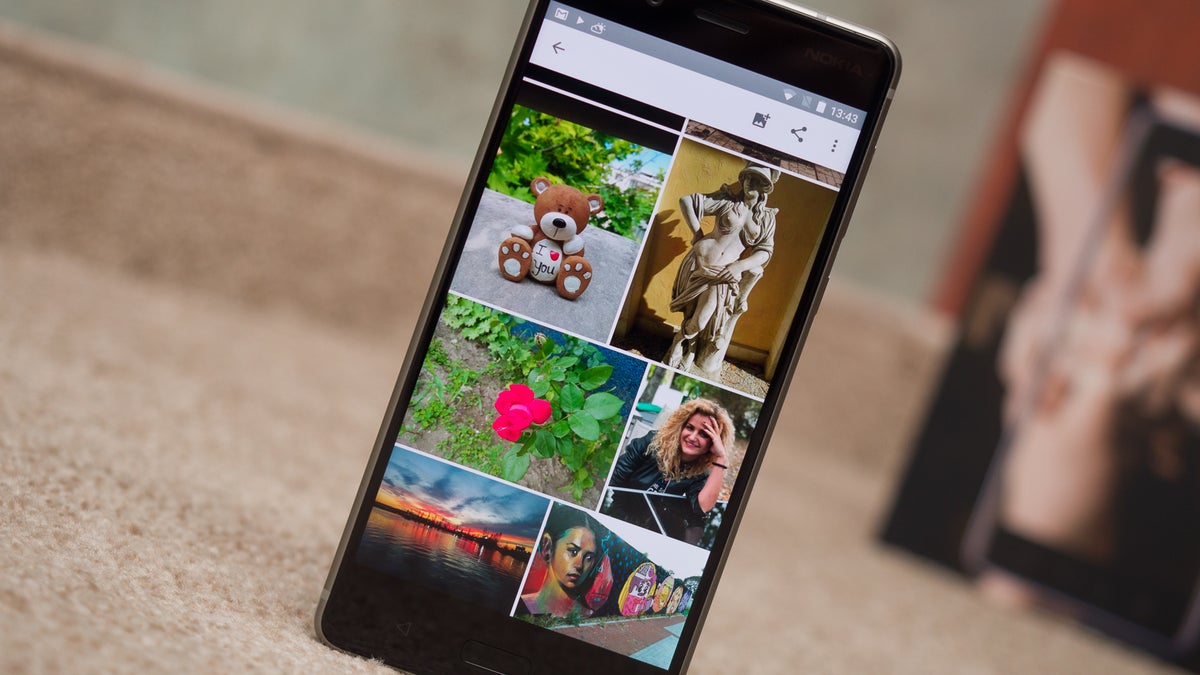
Luckily, this was the case with a newly discovered potential point for exploits found by the Android security team. It was quite an unusual one too. According to the latest Android Security Bulletin, the vulnerability “could allow a remote attacker using a specially crafted PNG file to execute arbitrary code within the context of a privileged process”.
Now let’s break it down. PNG files, for those unfamiliar with the format, are used for images or photos and are commonly used because of the better way they handle compression compared to JPG files. This means they are easily shareable between users through various messaging apps. According to the report, it was possible for a proficient enough coder to attach code to the image file that would be executed once the user opens it. The code would also be able to access the main processes of the operating system and potentially change them in a way that is beneficial for the attacker.
If that sounds scary, it’s because it is. Unauthorized root access to a device can cause all sorts of trouble for the user. Luckily, the issue was found before any reports of the vulnerability being put to practical use came in and a fix is being provided with the latest security patch for Android. Security updates dated 2019-02-05 or later include the fix for this vulnerability.
Of course, the security team isn’t releasing any specific information about how the exploit could work, making sure owners of devices that receive security updates slower are as safe as possible.













Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: