Long-running major vulnerability left millions of Android handsets wide open to data theft

According to a tweet from Google's Łukasz Siewierski (via Mishaal Rahman, 9to5Google), hackers and "malicious insiders" have been able to leak the platform signing keys used by several Android manufacturers to sign system apps used on Android devices. These signing keys are used to guarantee that the apps and even the Android operating system version running on your phone, are legitimate.
Long-running vulnerability affected LG, Samsung, and other Android-related manufacturers
Baked into Android is a system that trusts apps signed by the same key that is used to authenticate the operating system itself. So you can see what the problem is here. A bad actor with control of these keys could have Android "trust" malware-laden apps on the system level. That is like giving a thief the keys to your home and car with your approval. Any and all data on vulnerable devices could be at risk. And some of these keys are used to sign regular apps installed from the Play Store or sideloaded from other Android app storefronts.
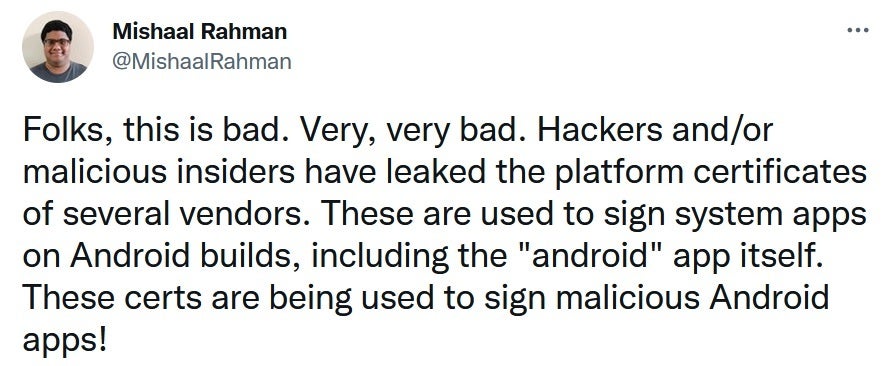
There's no beating around the bush when it comes to this vulnerability.
Rahman tweets that the leaked signing keys cannot be used to install over-the-air updates that are compromised. And he adds that the Play Store Protect system could flag apps signed by the leaked keys as being potentially harmful.
While all of the sources of the leaked keys have yet to be identified, the companies that have been named include the following:
- Samsung
- LG
- Mediatek
- Szroco (the company that produces Walmart's Onn tablets)
- Revoview
Google says that the vulnerability was reported to it in May of this year and that the companies involved have "taken remediation measures to minimize the user impact." Not exactly the "all clear" sign, especially in light of the news that APK Mirror has very recently come across some of the vulnerable signing keys in Android apps from Samsung.
Google, in a statement, says that Android users were protected through the Google Play Store Protect feature, and through actions taken by manufacturers. Google stated that this exploit did not impact any apps downloaded from the Play Store.
A Google spokesperson said, "OEM partners promptly implemented mitigation measures as soon as we reported the key compromise. End users will be protected by user mitigations implemented by OEM partners. Google has implemented broad detections for the malware in Build Test Suite, which scans system images. Google Play Protect also detects the malware. There is no indication that this malware is or was on the Google Play Store. As always, we advise users to ensure they are running the latest version of Android."
What you need to do to limit your exposure
Google is recommending that the companies involved swap the signing keys currently being used and to stop using the ones that leaked. It also suggests that each firm initiate an investigation to understand how the keys were leaked. Hopefully, this would prevent something like this from happening again in the future. Google is also recommending that companies use singing keys for the minimum number of apps to reduce the number of potential leaks in the future.
So what can you do as the owner of a possibly affected Android phone? Make sure that your handset is running the latest version of Android and install all security updates as soon as they arrive. Who cares if these updates don't bring exciting new features as their job is to make sure that your device doesn't get compromised. And Android users should refrain from sideloading apps. That is when you install an app sourced from a third-party app storefront.
The scary thing is that this vulnerability apparently has been around for years. Samsung even brings this up in its statement made to Android Police which says, "Samsung takes the security of Galaxy devices seriously. We have issued security patches since 2016 upon being made aware of the issue, and there have been no known security incidents regarding this potential vulnerability. We always recommend that users keep their devices up-to-date with the latest software updates."












Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: