Another iOS-threatening malware replaces apps and steals sensitive information

It seems iOS is having a bad month – last week, there was the WireLurker scare – a malware that is capable of infecting even the previously-deemed-safe non-jailbroken devices. Apple says it's got a handle on that, but, to be fair, WireLurker was only able to infect users who connected their phone to their PC via USB and attempted to sideload apps from a 3rd party app store.
Today, we hear about something a bit scarier. It's called a "Masque Attack" and what it does is, it installs a malicious app on one's iOS device and masks it to look like any other app, legitimately installed from the App Store.
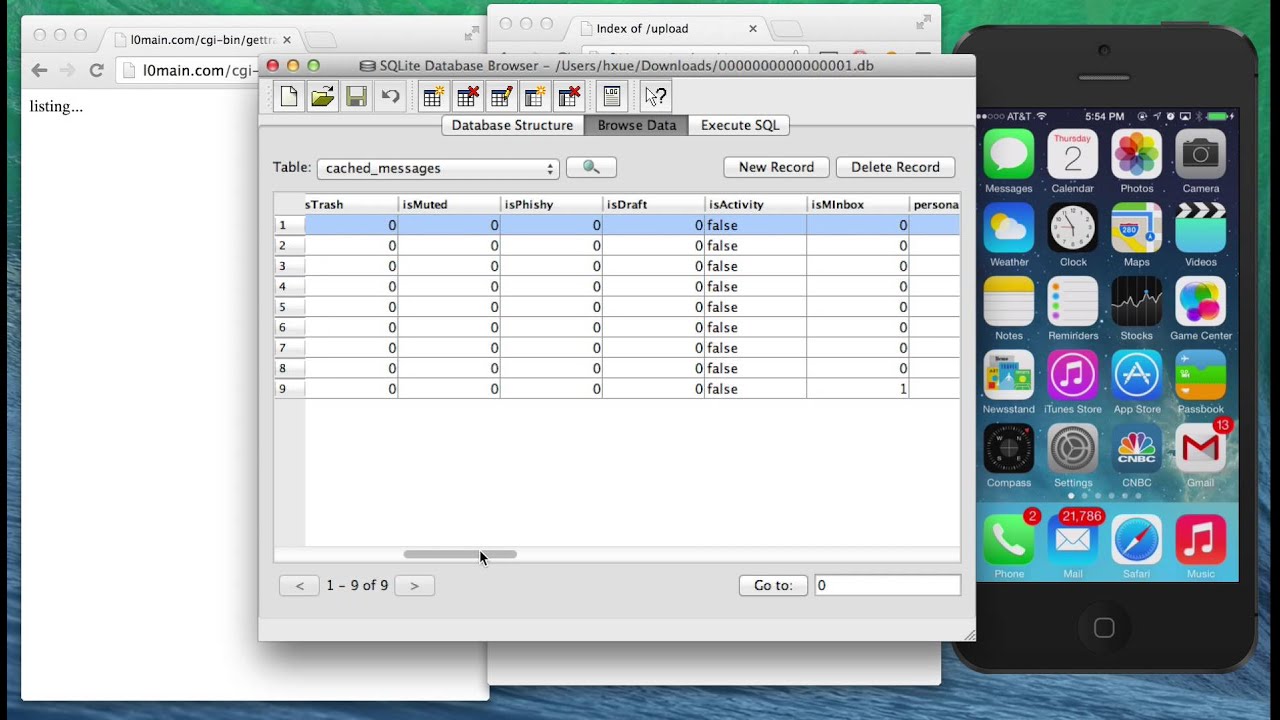
From there, attackers have a few options – they can mimic an essential app's login interface and steal a users' sensitive credentials; they can also replicate an email app, which will still allow the user to enter and read his inbox – the attackers will gain access to those emails, too; they can also use Masque as a way to bypass the app sandbox and get root privileges.
The way a Masque Attack slips into one's system is via an installation from a 3rd party website – the attacker will attempt to bait the victim into visiting a website, which will open a pop-up request to install an app. If the user accepts – the malware is in, hidden under whatever app it's supposed to act as. Masque Attack can mimic any legitimate app, on both jailbroken and non-jailbroken devices, as long as it's not iOS pre-installed (Safari, Apple's email client, etc.).
So there you go kids – watch out for suspicious popups, and don't install things from 3rd party websites, not even iOS is safe nowadays.
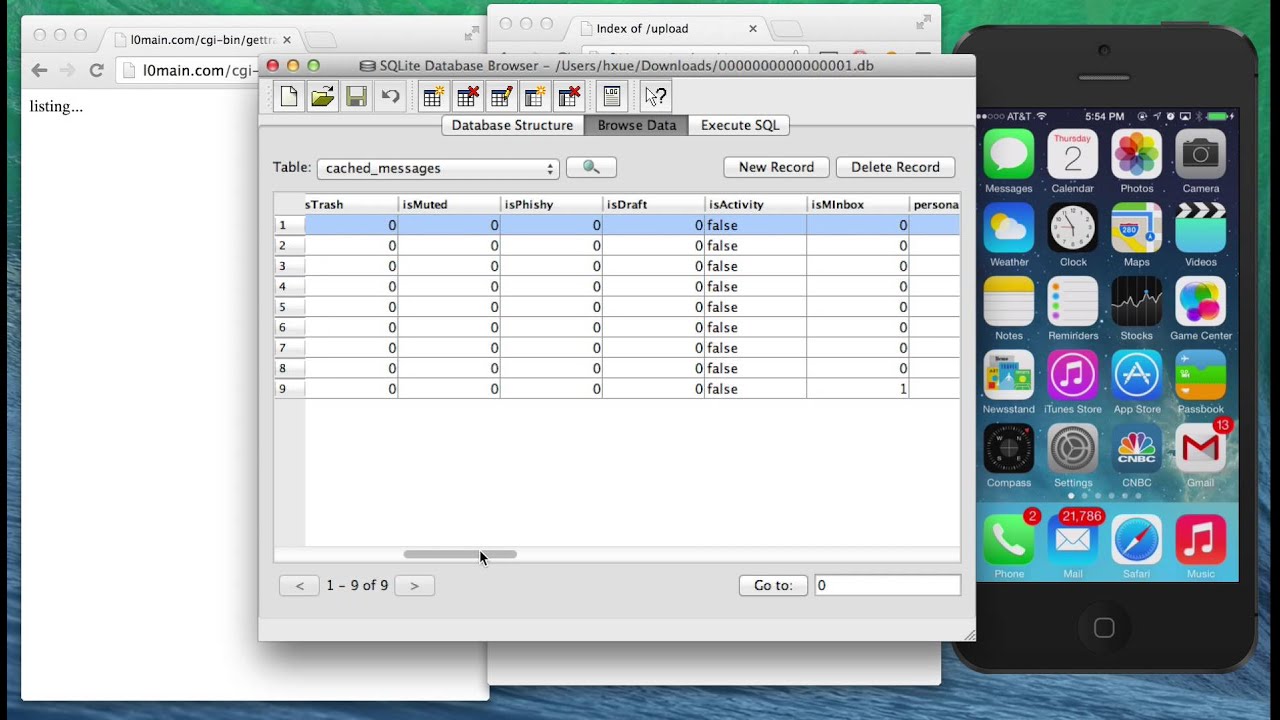
From there, attackers have a few options – they can mimic an essential app's login interface and steal a users' sensitive credentials; they can also replicate an email app, which will still allow the user to enter and read his inbox – the attackers will gain access to those emails, too; they can also use Masque as a way to bypass the app sandbox and get root privileges.
So there you go kids – watch out for suspicious popups, and don't install things from 3rd party websites, not even iOS is safe nowadays.
source: FireEye via Digital Trends













Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: