Android users are getting caught up in toll fraud which uses malware to hike their telecom bills

A fresh report from Microsoft Security says that Android users are getting attacked by malware that signs up unsuspecting phone owners to expensive premium services that they didn't request or subscribe to. The victim is left holding the bag at the end of the day as the malware adds these charges to his or her monthly telecom bill. Since no one wants their handset to be cut off, these payments are usually made without questioning them, although many victims don't even bother looking over their phone bills every month.
Because this attack relies on a cellular network to do the dirty business, the malware might disconnect you from Wi-Fi or use other means to force you onto your cellular network. Once a connection to a cellular network is made, the malware starts the process of subscribing to premium services and will even steal a one-time password (OTP) sent to verify your identity. Any notification sent to show that you've signed up for a subscription service is suppressed to keep the deed hidden from the victim so that he or she doesn't unsubscribe.
Such malware-laden apps hide as wallpaper apps, messaging apps, and apps that "clean" the inner workings of your phone
The attackers seek to infect as many phones as possible while keeping their apps listed in the Google Play Store for as long as possible. These apps usually are listed under popular categories such as personalization (wallpaper and lock screen apps), beauty, editor, communication (messaging and chat apps), photography, and tools (like cleaner and fake antivirus apps).
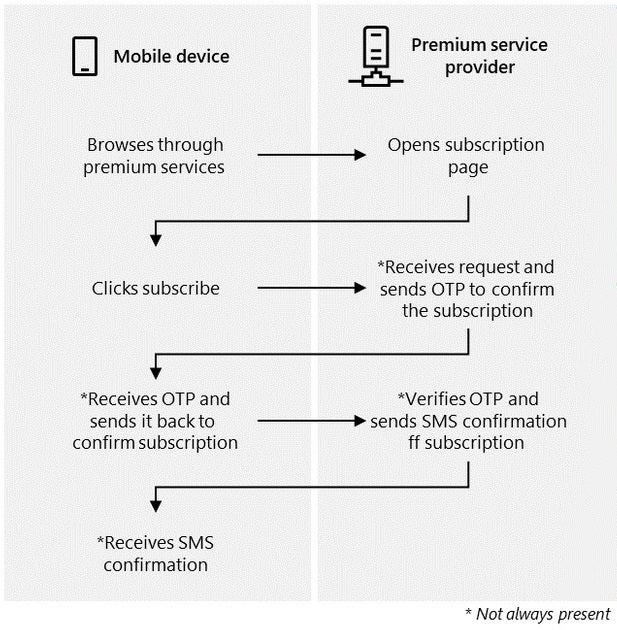
How a malware-infected app might sign you up for high-priced subscription services you didn't ask for
These apps not only ask for a large number of permissions, some of the permissions asked for also don't make sense. For example, a wallpaper app containing malware might ask for permission to access your SMS apps. That is not a permission that such an app would normally need.
Many of these malware-laden apps share the same UI, icons, and buttons. In the developer profile, look for fake developer names and fake email addresses. In the listing, watch out for spelling mistakes and poor grammar.
Even though Google allows you to, do the smart thing and refrain from sideloading apps on your Android phone
The bottom line is that this malware results in victims having to pay significantly higher mobile invoices after getting charged for premium services they didn't sign up for. And because these apps can escape detection, a huge number of them can be installed before the attack is discovered. This malware belongs in a category known as toll fraud, which accounted for 34.8% of installed "Potentially Harmful Application" (PHA) from the Google Play Store in the first quarter of 2022, second only to spyware.
If there is a suggestion that we can make, do not sideload apps on your Android phone even though Google allows you to do so. When you sideload an app, you are installing it from an unofficial app store. For example, any time you install a third-party app on your Android device that wasn't sourced from the Google Play Store, that would be considered sideloading.
Look for signs that you've installed an app with malware. These signs include rapid battery drain, connectivity issues, phone overheats constantly and is running much slower. Be on the look out for a large number of pop-up ads. And double check your mobile bill every month and look for chargers for services that you don't remember subscribing to. If you detect any of these red flags, you need to contact your carrier immediately.
Keep in mind that once you've been ensnared in this trap, getting your money back from your carrier is unlikely. So the sooner that you can recognize that you've been had, the better it is for you.











Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: