Over 100 million Americans had their personal data exposed in major text data breach

What we are going to tell you is something that is bound to get your mind thinking back about any embarrassing texts you might have written. Or whether you might have sent some personal information via text like your social security or credit card numbers, passwords or even PINs. According to vpnMentor (via USA Today), a company that ranks virtual private networks (VPN), a database containing millions of text messages has been breached.
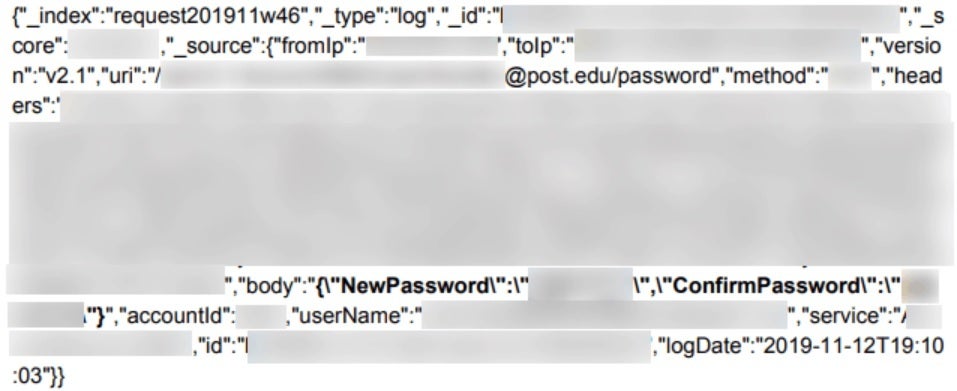
The database belongs to an American outfit named TrueDialog. The latter provides "Enterprise-Grade SMS Texting Solutions." The information available from the breached database not only includes tens of millions of texts from hundreds of millions of American users, it also contained millions of usernames, passwords (some in cleartext, others encoded but easy to decrypt) and more. The report puts the blame for the data breach directly on TrueDialog for failing to protect the database. It also notes that discovering the identity of the database owner was not difficult.
Over 100 million American citizens could be impacted by this data breach
The number of people affected by the breach is huge and the possibility that these texts could be read by bad actors is a very major deal; that puts companies like TrueDialog on the defensive. As vpnMentor notes, "Some affected parties deny the facts, disregarding our research or playing down its impact. So, we need to be thorough and make sure everything we find is correct and true. In this case, it was quite easy to identify TrueDialog as the database owner. Their host ID “api.truedialog.com” was found throughout. However, it was also clear that this was a huge data breach, compromising the privacy and security of over 100 million U.S. citizens across the country."
The database is hosted by Microsoft Azure and runs in the U.S. on the Oracle Marketing Cloud. It contains 1 billion entries adding up to 604GB of data. This data includes information about TrueDialog's business, its business clients and the latter's customers. All of this information could have been used by bad actors to steal identities and money from those with information exposed in the breach. Additionally, all of this data could have been sold to marketers and scammers. Knowing all of this information would make it easier for bad actors to engage in phishing schemes.
Hundreds of millions of American citizens could have been impacted by the data breach
Perhaps you have yet to understand the seriousness of this. Tens of millions of SMS messages that were sent via TrueDialog were leaked revealing the full names of message recipients, account holders and users of TrueDialog's services. But even worse, the content of messages, email addresses, and recipients' phone numbers were viewable along with the date and time that these messages were sent.
TrueDialog itself could face a negative backlash because of this leak. The company's reputation will take a hit and companies that pay it for providing leads will stop doing business with it if they fear that those leads will get leaked for free. And the amazing thing is that vpnMentor was able to discover the breach because the database was not only unsecured, it also was unencrypted. TrueDialog has been in business for ten years, says vpnMentor, works with more than 990 cellphone operators and reaches 5 billion subscribers globally.











Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: