According to a new research paper, authored by security researchers from several institutions, including CSIRO and UC Berkeley, Android users who use free VPN apps are at a high risk of security intrusions. A number of such applications have been found to include adware and trojans, along with user tracking libraries and traffic interception mechanisms, while some of them also do not provide encryption of any kind.
A VPN, short for a virtual private network, is a commonly used type of security service which, in theory, allows an end user to surf the internet anonymously, bypassing third-party monitoring or censorship. It works by redirecting (and most commonly encrypting) user traffic through a remote server, which incurs a speed penalty, but provides more security in return. However, the study, which analyzed free VPN services for Android, found that a large amount of apps feature troubling behavior which exposes end users to potential risks.
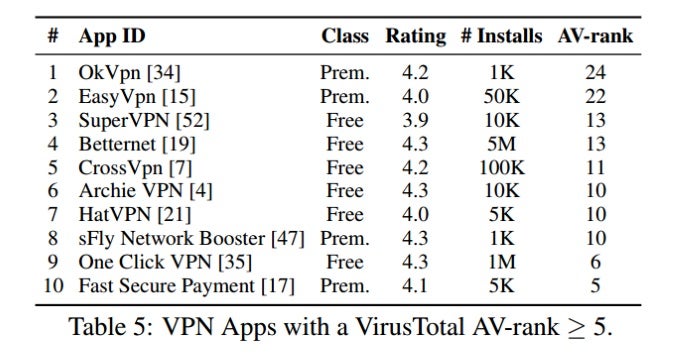
An analysis of VPN services through the online service VirusTotal returned a list of several apps which have more than 5 positives when tested for viruses, with the two worst offenders, OkVpn and EasyVpn having 24 and 22 hits respectively. The most commonly found type is adware, which typically replaces third-party ads on webpages with its own, more intrusive ones. 18 percent of free VPN apps were found to not encrypt user traffic at all, opening up the possibility of snooping, particularly when connected to a public network. The majority of free apps also do not fully tunnel traffic, leaving some critical data exposed. Two services, HotspotShield and WiFi Protector VPN, were found to inject tracking scripts into webpages, while the former also redirected traffic to e-commerce sites such as eBay and Alibaba through partner websites, letting it make money from users’ purchases. Four apps were also caught using illegitimate self-signed certificates, which give them access to all encrypted traffic on a given device.
The study also made a point of analyzing user awareness of intrusions to their privacy and found that, on average, most users have not expressed public concern about their security when using a VPN service. This is particularly troubling, as it leads to the conclusion that users either do not notice, or simply don’t care when an application requests sensitive permissions, such as handling text messages, which is a requirement imposed by the OS.
Some things to keep in mind about the study, however, include the fact that analyzed apps were collected last year, and as a result some of the worst offenders on the list can no longer be found on the Play Store. Also, not all of these security problems are necessarily malicious in intent – some may be just programming errors, while others have been confirmed by the app developers to be intended features. Also worth noting is the fact that paid VPN services were not analyzed as part of this study, and neither were iOS apps of any kind, leaving them innocent until proven otherwise.
source:
CSIRO Research via
The Verge













Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: