HP study finds that there's no such thing as a secure smartwatch
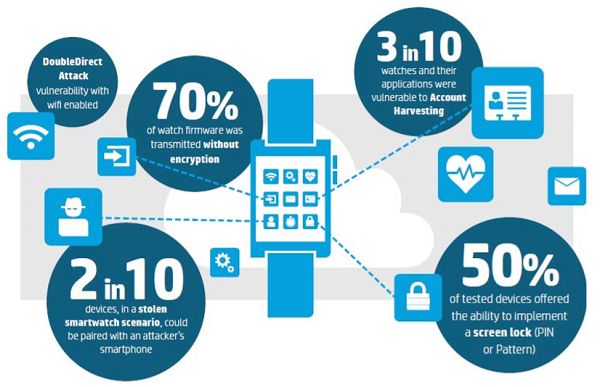
70 percent of the tested smartwatches have hidden vulnerabilities in the way that they receive firmware updates. Fortunately, the updates are digitally signed, meaning that hackers cannot install altered firmware. On the downside, hackers can download these insecure updates and analyze them in order to find other vulnerabilities that they can exploit.
As smartwatches continue to get traction in both consumer and business sectors, these vulnerabilities will have to be fixed in order to make sure that hackers aren't simply being pointed towards a new wide-open door they can sneak through. There's no better time to act on these security threats and create secure protocols and systems than now, before the entire Internet of Things trend blows into full scale. The general consensus among analysts is that the IoT movement will give us the option to manipulate not only devices, but also our cars, and even our homes on the go. At the moment, however, it looks like the added connectivity comes with a grave security risk.
source: HP via The Register










Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: