University study with video: Viber user data pretty much wholly unencrypted and easily accessible

If you are one of Viber’s few hundred million users, your Viber life is an open book, from messages, to pictures and video, to location data, the whole stream is unencrypted, and the server side appears to have no authentication either.
Moreover, the activity is stored on Viber’s servers, not deleted, and can be accessed without any credentials according to researchers at the University of New Haven’s Tagliatela College of Engineering, in Connecticut.
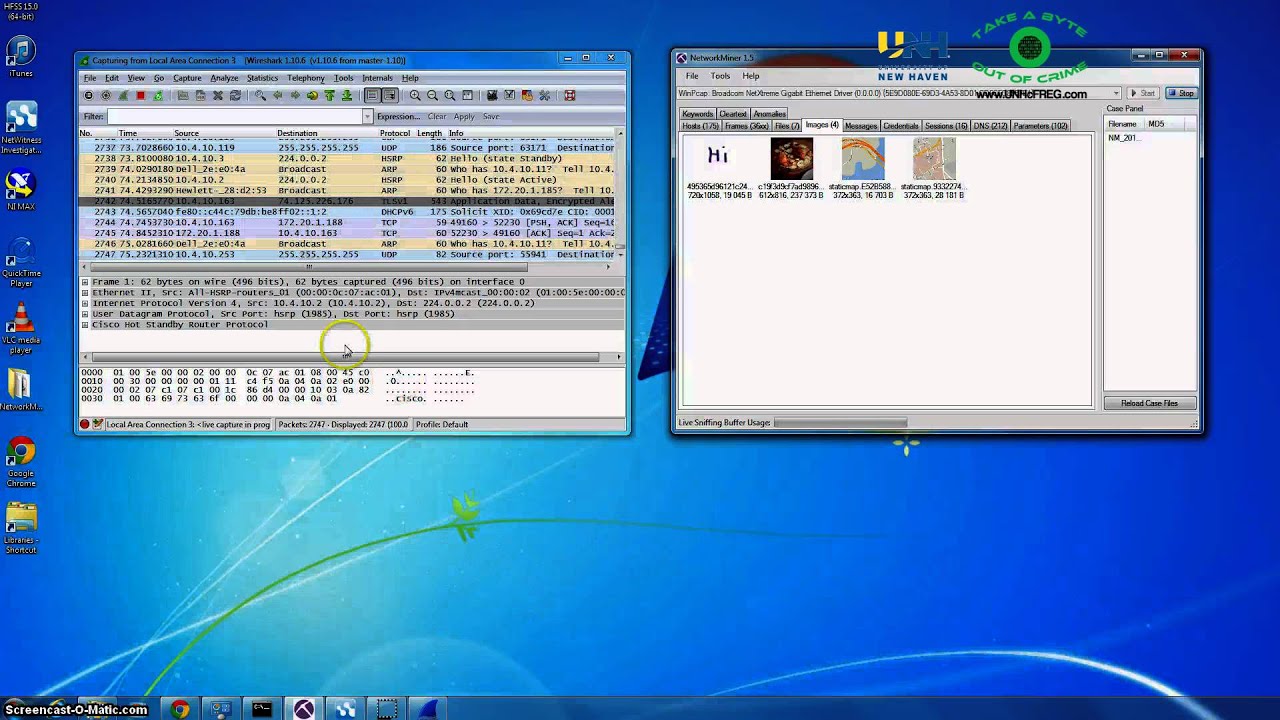
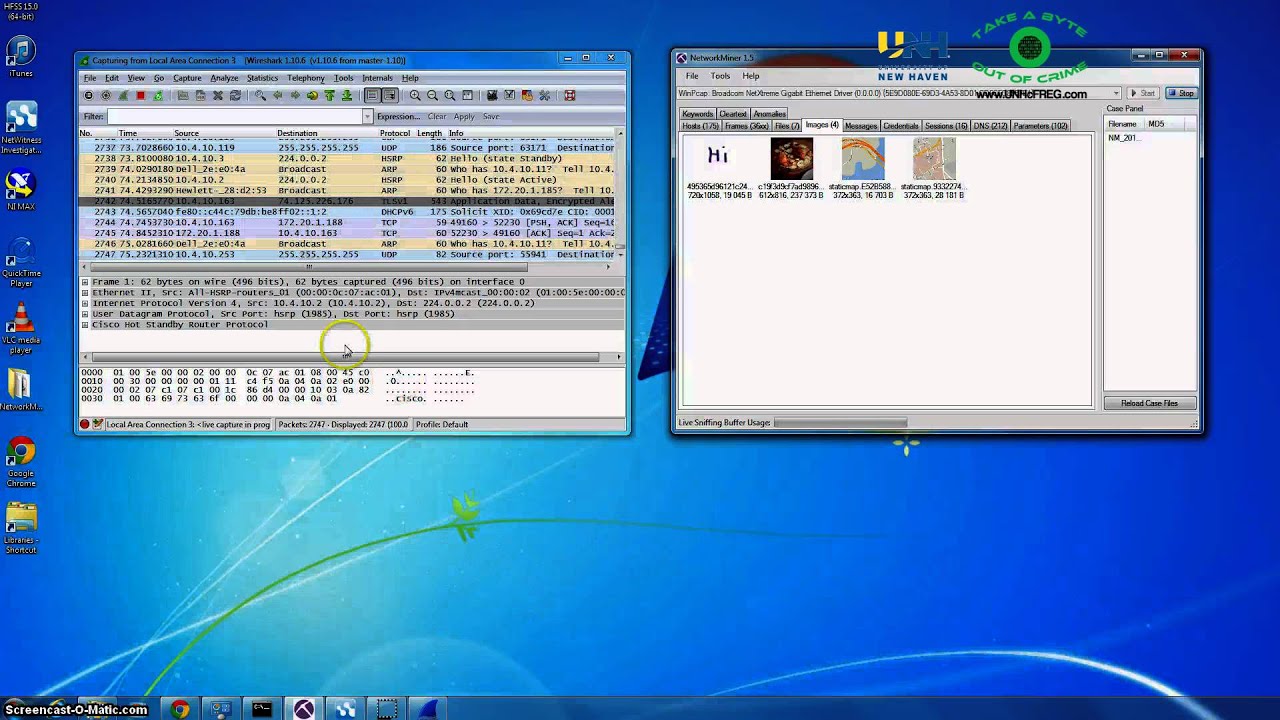
Researchers with the Cyber Forensics Research & Education Group were able to grab pictures, videos, even doodles sent through Viber. They set up a Windows PC as a wireless access point and then were able to monitor traffic between two Android smartphones, only one of which was connected to that access point. The other device was on the traditional carrier network. The intercepting and capture of data was happening in real time, as you can see in the video below.
“The data is stored on Viber's server in an unencrypted manner. There is also no authentication method used, so anybody who has access to these links can look at this data, retrieve this data, and do whatever they want with it.”
Dr. Ibrahim Baggili and Jason Moore are the researchers at University of New Haven that brought this issue to light. The duo also noted that WhatsApp apparently does not encrypt user-location data, but that issue was nothing like the gaping hole uncovered with Viber. The team then went back to Viber's server a few days later and found the data was still there, unencrypted and accessible with no authentication or credentials.
Viber has apparently fixed the issues, with updates to the Android and iOS apps on the way, but no word about all the other platforms Viber operates on, Windows, Windows Phone, BlackBerry, BadaOS, and Symbian. The company states that it is not aware of any single user affected by this issue.
In this day and age though, how does anything that is network connected get created without some reasonable type of data protection in mind? It is disappointing to say the least that the company had to fix anything at all.
sources: CNET, Naked Security and University of New Haven
Researchers with the Cyber Forensics Research & Education Group were able to grab pictures, videos, even doodles sent through Viber. They set up a Windows PC as a wireless access point and then were able to monitor traffic between two Android smartphones, only one of which was connected to that access point. The other device was on the traditional carrier network. The intercepting and capture of data was happening in real time, as you can see in the video below.
Dr. Ibrahim Baggili and Jason Moore are the researchers at University of New Haven that brought this issue to light. The duo also noted that WhatsApp apparently does not encrypt user-location data, but that issue was nothing like the gaping hole uncovered with Viber. The team then went back to Viber's server a few days later and found the data was still there, unencrypted and accessible with no authentication or credentials.
In this day and age though, how does anything that is network connected get created without some reasonable type of data protection in mind? It is disappointing to say the least that the company had to fix anything at all.
sources: CNET, Naked Security and University of New Haven













Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: