More than 300 Play Store apps found to be using devices as clickfarms
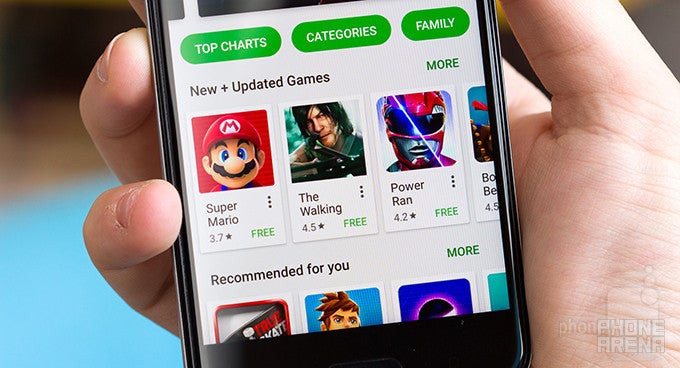
The numbers associated with this kind of malware are impressive, too: more than 300, with a cumulative 4–14 million installs. The apps themselves are mostly live wallpapers or simple utilities — the researchers specifically pointed the finger at the following app developers: Attunable, Classywall, Firamo, FlameryHot, NeonApp, Goopolo, Litvinka Co, Livelypapir, Tuneatpa Personalization, Waterflo, X Soft, and Zheka.
The research comes from ad fraud detection agency eZanga, who claims to have immediately notified Google of the malicious apps. And while Google has historically been quick to take action in similar occasions, it seems clear its current malware detection practices aren't working as well as they should be.












Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: