Android users: under no condition should you sideload this spyware on your phone!
Software security firm Zimperium says that a sophisticated new malicious Android app, posing as a System Update application, can create havoc with your phone-and with your life. The app can turn control of your Android phone over to bad actors who will be able to steal messages, data, images, take photos, go through your browser history, record phone calls and audio, view your WhatsApp messages and much more. This is indeed a serious exploit.
Do not sideload this app on your Android phone!
The System Update app has never been in the Google Play Store, a fact confirmed by Google. zLabs researchers discovered the app and after conducting an investigation, it was discovered that it was a sophisticated spyware campaign with complex capabilities. Now we know exactly what you're thinking. How long will it take Pizza Hut to deliver a green pepper, onions and pineapple pizza? The second thought on your mind is that if the app has never been listed in the Google Play Store, how did it get installed on your Android phone? The answer is simple, actually. It was installed by sideloading a malicious app from a third-party app store.
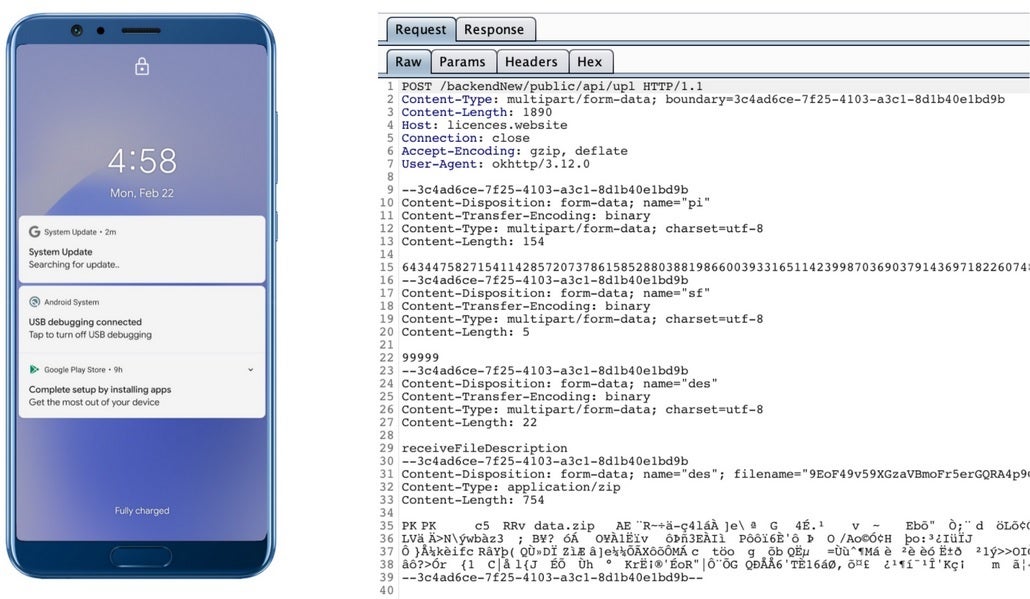
The notification on the phone in this picture is from the spyware, not the app
Once the app is installed, "the device gets registered with the Firebase Command and Control (C&C) with details such as the presence or absence of WhatsApp, battery percentage, storage stats, the token received from the Firebase messaging service, and the type of internet connection." The spyware is triggered when multiple conditions take effect such as the addition of a new contact, the receipt of a new SMS, or the installation of a new app. The spyware is always looking for something to, well, spy on. If it detects that a phone call is taking place it will record the conversation, add the updated call log, and store the information to a command and control (C&C) server as an encrypted ZIP file. To make sure that there are no traces of what happened, the spyware deletes the files as soon as it receives a thumbs up from the server stating that the files have been received.
The data is then placed into several folders in the spyware's private storage. One characteristic of the spyware is that it always wants fresh data. For example, if the malicious software is set to collect a new photo after 40 minutes, that is exactly what will happen. Location data is collected via GPS or through the network depending on which one has more recent data. If the current data is more than five minutes old, the location data is collected and stored once again.
The spyware will create a fake notification if the infected device's screen is off when a command is received using the Firebase messaging service. of the things that this spyware does includes stealing thumbnails of images and video.
There is no doubt that this is a dangerous app. Perhaps the best thing you can do is stay away from sideloading an app called "Software Update." Or you might want to consider staying away from third party app stores altogether. After all, check this list of things that this malicious app can do:
- Steal instant messenger messages;
- Steal instant messenger database files (if root is available);
- Inspect the default browser's bookmarks and searches;
- Inspect bookmark and search history from browsers such as Google Chrome, Mozilla Firefox, and Samsung Internet Browser;
- Search for files with certain extensions such as.pdf, .doc, .docx, and .xls, .xlsx;
- Inspect data from the clipboard;
- Inspect the content of notifications;
- Record audio and phone calls;
- Take pictures on a timed basis through the front or back cameras;
- Create a list of installed apps;
- Monitor the GPS location;
- Steal SMS messages; phone contacts, images & videos, and call logs;
- Removing device information device such as installed applications, device name, and storage stats; and
- hiding the icon from the device's app drawer and menu.
You can see why it is important to avoid this app at all costs.













Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: