Mobile malware getting out of control? Study claims 614% increase on year, Android accounts for 92% of total infections

A terrifying report was released two days ago by the Mobile Threat Center arm (MTC) of Juniper Networks – a manufacturer of network equipment with a hefty stake in enterprise security. According to Juniper, its MTC research facility is dedicated to 'around-the-clock mobile security and privacy research'. The MTC found mobile malware growing exponentially at an alarming rate – a 614% on year increase reaching a total of just about 280,000 malicious apps.
The report goes on to state that according to their research, Android is the main culprit in the vast expansion of the nefarious activity – it grew from accounting for 24% of all mobile malware in 2010 to 92% by March this year. And if you won't take the MTC's word for it, separate studies by McAfee (February - 97%) and F-Secure (May – 91.3%) from this year seem to agree on the ballpark of total incidences related to Android.
Reading through the report, we extracted what appear to be the main factors contributing to Android's unflattering No.1 spot.
Those are all pretty big statements. If you're wondering what the basis for such devastating results is, the MTC also reports that the sample they used was acquired first-hand and is based on the analysis of over 1.85 million mobile applications and vulnerabilities. The center asserts that this is one of the largest quantitative studies of its kind and completely eclipses their previous one by using 133% more data.
Don't forget, however, that some of those companies may have more carnal reasons to be overplaying the threats. Nevertheless, with multiple sources pointing in the same direction, there sure appears to be a reason to worry.
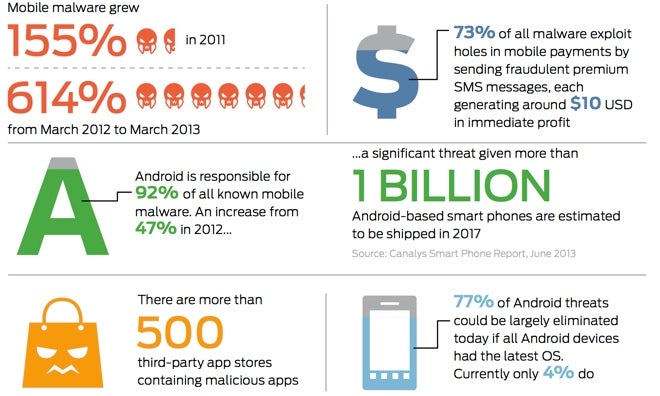
Need help processing all of this? The infographic by MTC bellow neatly summarizes some of the important findings:
- We seem to talk a lot about fragmentation when referring to Android, and security appears to be no exception. Google's own numbers as of June 3, 2013 reveal that only a measly 4% of Android phone users ran the latest version of the operating system. As much as 77% of the most popular types of malware intrusions could have been avoided if everybody ran the latest Android OS, the MTC claims.
- The Juniper devision identified over 500 third-party Android app stores worldwide, known to be hosting a wide berth of nasty code. In their sample, on average 3 out of every 5 such stores originated from either China or Russia
- According to the research, malware developers have taken a decidedly for-profit direction, turning attacks into a business. Moreover, the MTC says each successful attack can yield about $10 on average in immediate profit. How? Their sample shows 73% of overall mobile malware attacks were FakeInstallers or SMS Trojans that exploit holes in mobile payments.
Those are all pretty big statements. If you're wondering what the basis for such devastating results is, the MTC also reports that the sample they used was acquired first-hand and is based on the analysis of over 1.85 million mobile applications and vulnerabilities. The center asserts that this is one of the largest quantitative studies of its kind and completely eclipses their previous one by using 133% more data.
"There's no doubt mobility will continue to be a pervasive and disruptive force across every industry. We have found that it has created an easy business opportunity for malware developers who are becoming savvy in their approach to quickly turn profits in a rapidly growing market. We anticipate that similar to the evolution of PC-based threats, mobile attacks will continue to increase and become more sophisticated in the coming years." - Troy Vennon, director of the Mobile Threat Center, Juniper Networks
Don't forget, however, that some of those companies may have more carnal reasons to be overplaying the threats. Nevertheless, with multiple sources pointing in the same direction, there sure appears to be a reason to worry.
Need help processing all of this? The infographic by MTC bellow neatly summarizes some of the important findings:












Things that are NOT allowed: